Preventing threat actors from taking advantage of Bloodhound 3.0, by Biju Varghese, AttivoTechBlogs
Por um escritor misterioso
Last updated 10 novembro 2024
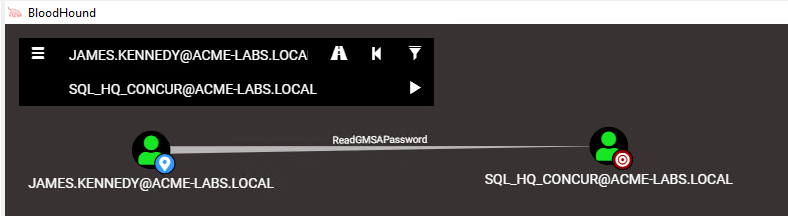
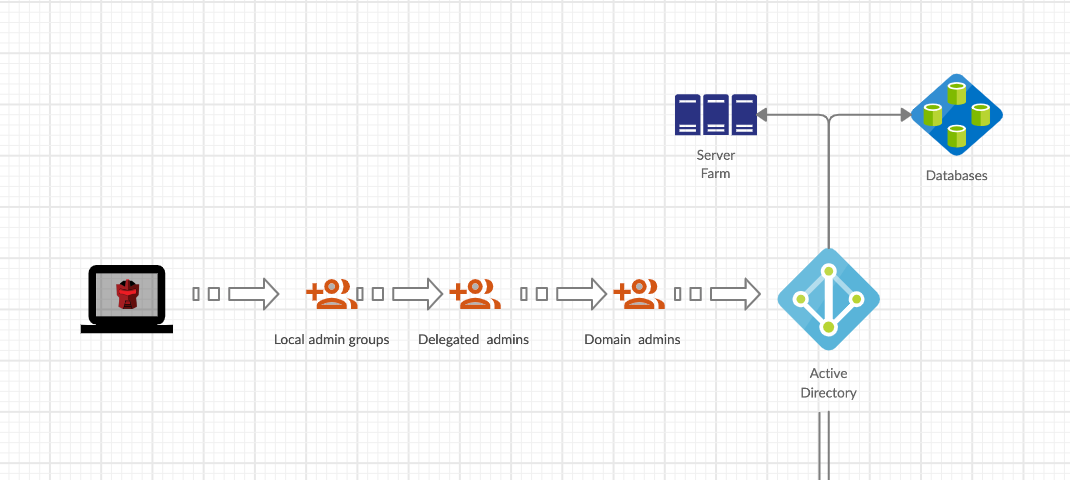
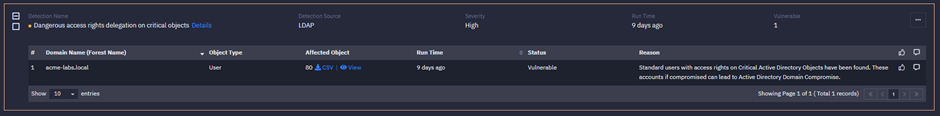
Bloodhound 3.0 with three new attack methods — GMSA Control, OU Control & SID History. This article discusses how one can protect one’s Active Directory
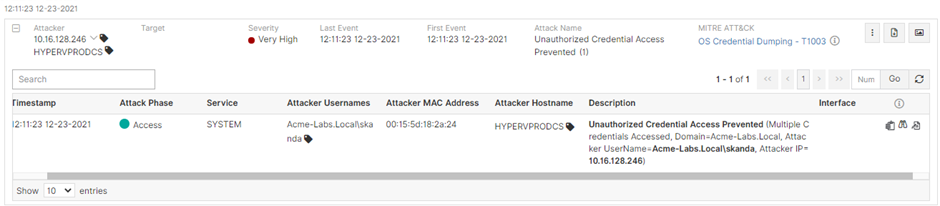
Preventing samaccountname spoofing and kdc bamboozing
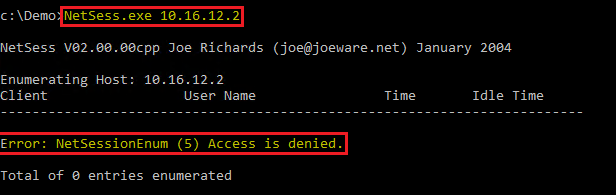
Lateral Movement Using SMB Session Enumeration
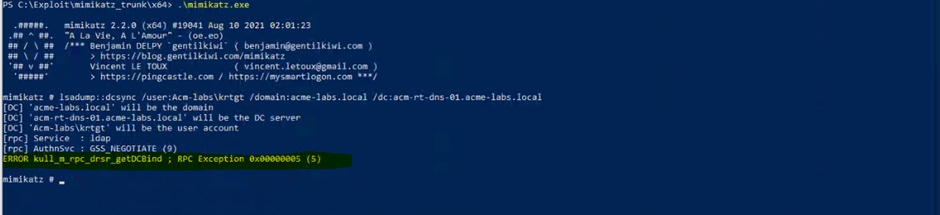
Preventing samaccountname spoofing and kdc bamboozing

Latest stories published on AttivoTechBlogs – Medium
Top stories published by AttivoTechBlogs in 2020 – Medium
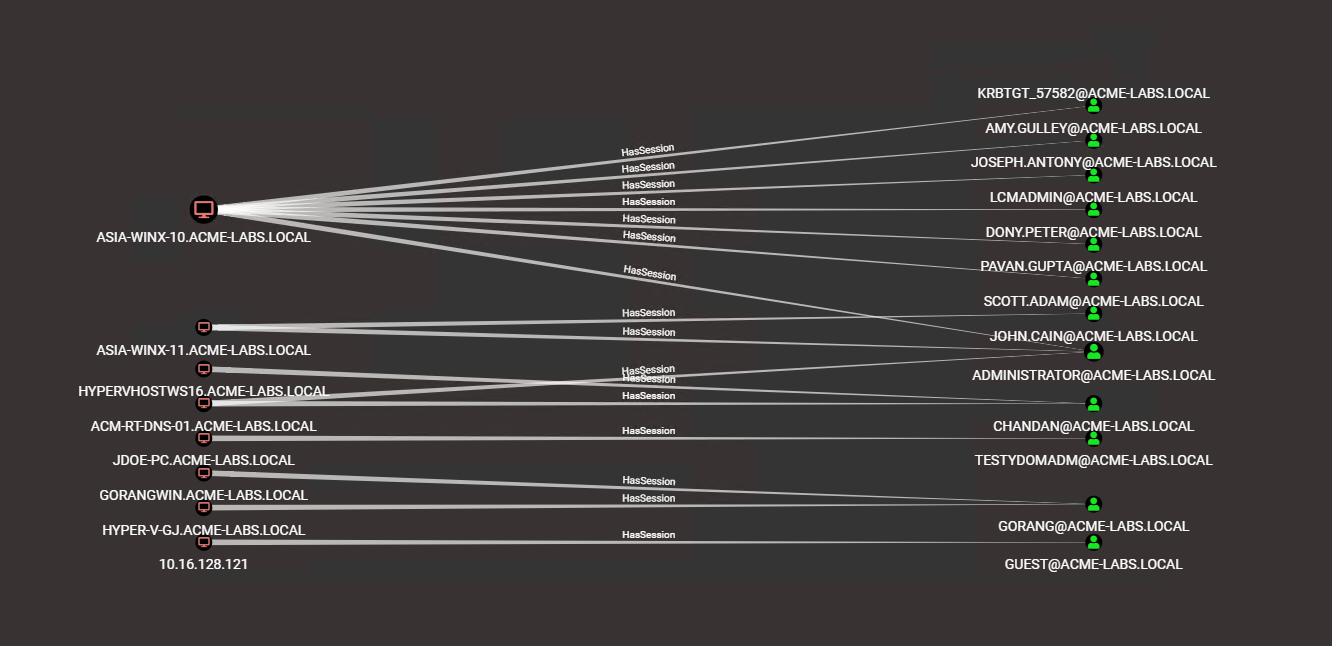
Lateral Movement Using SMB Session Enumeration

Latest stories published on AttivoTechBlogs – Medium
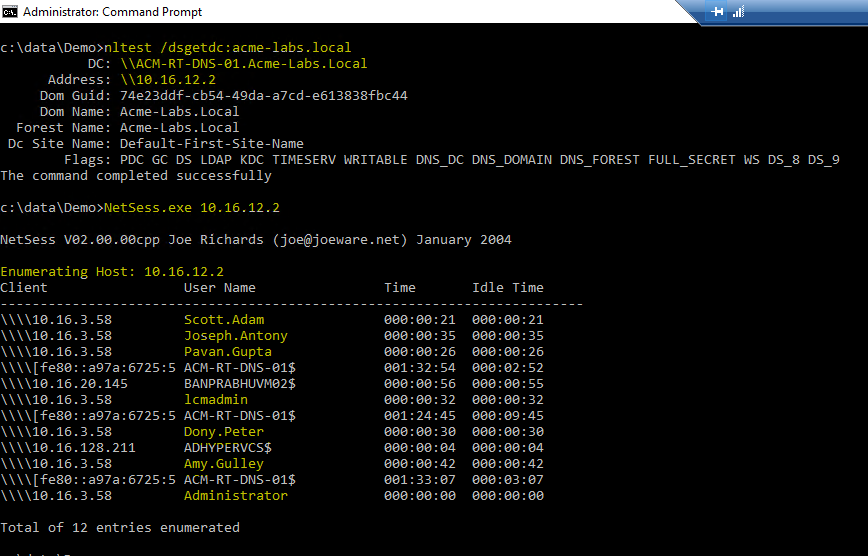
Lateral Movement Using SMB Session Enumeration
Preventing samaccountname spoofing and kdc bamboozing

AttivoTechBlogs – Medium
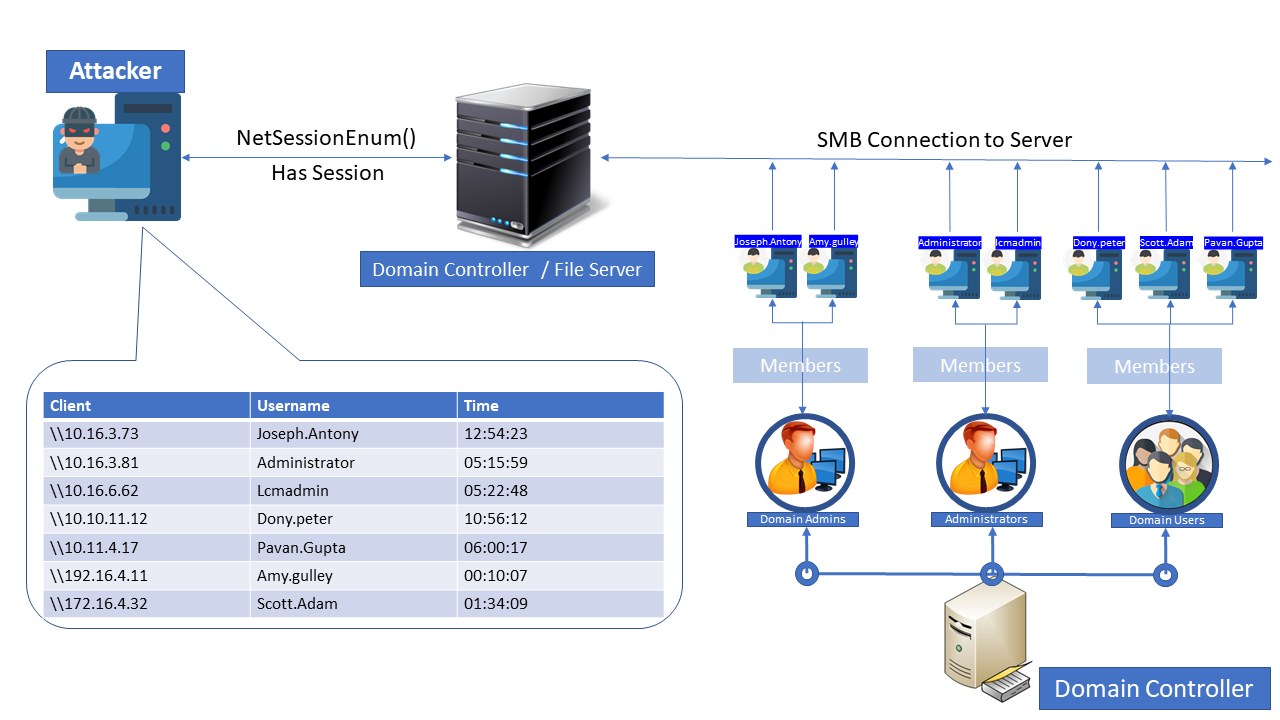
Lateral Movement Using SMB Session Enumeration
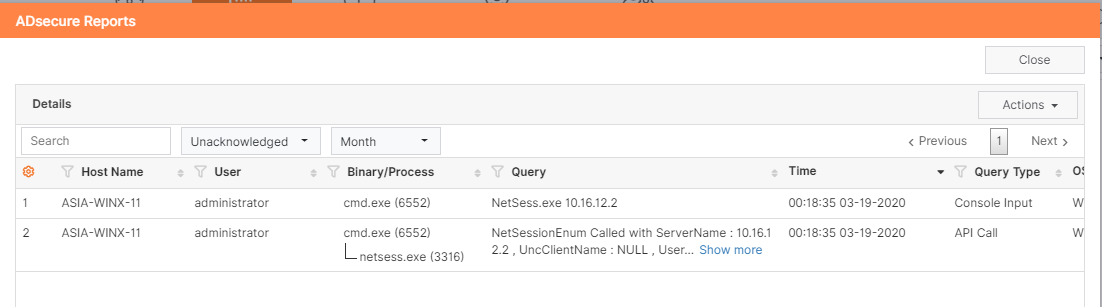
Lateral Movement Using SMB Session Enumeration
Recomendado para você
-
 GTA: San Andreas: todos os códigos do jogo para PS2, PS3, PS4 e PS510 novembro 2024
GTA: San Andreas: todos os códigos do jogo para PS2, PS3, PS4 e PS510 novembro 2024 -
Codigo GTA San Andreas PS3, PDF, Transporte10 novembro 2024
-
 Códigos GTA 5: Veja Cheats Para Armas, Ficar Invencível e Mais10 novembro 2024
Códigos GTA 5: Veja Cheats Para Armas, Ficar Invencível e Mais10 novembro 2024 -
 GTA 5: Cheats e códigos para PS4, Xbox One e PC10 novembro 2024
GTA 5: Cheats e códigos para PS4, Xbox One e PC10 novembro 2024 -
Codigo GTA 5 Ps3 para Ativar No Controle10 novembro 2024
-
 Best Helicopter Tours, Las Vegas, Grand Canyon, Maui10 novembro 2024
Best Helicopter Tours, Las Vegas, Grand Canyon, Maui10 novembro 2024 -
 Par de Bieletas Traseira Para auto Hyundai Kia Sportage Original - Bieleta Estabilizadora - Magazine Luiza10 novembro 2024
Par de Bieletas Traseira Para auto Hyundai Kia Sportage Original - Bieleta Estabilizadora - Magazine Luiza10 novembro 2024 -
 Helicóptero 4 hélices controle 2.4G Giroscópio eletrônico de 610 novembro 2024
Helicóptero 4 hélices controle 2.4G Giroscópio eletrônico de 610 novembro 2024 -
 Códigos GTA 5: consiga armas, invencibilidade, aviões e mais!10 novembro 2024
Códigos GTA 5: consiga armas, invencibilidade, aviões e mais!10 novembro 2024 -
 GTA V para Xbox Series X Rockstar Games - Lançamento - Jogos de Ação - Magazine Luiza10 novembro 2024
GTA V para Xbox Series X Rockstar Games - Lançamento - Jogos de Ação - Magazine Luiza10 novembro 2024
você pode gostar
-
 NARUTO CIRCULAR TOPO DE BOLO (PAPEL FOTOGRÁFICO) - PAPEL ARROZ10 novembro 2024
NARUTO CIRCULAR TOPO DE BOLO (PAPEL FOTOGRÁFICO) - PAPEL ARROZ10 novembro 2024 -
 Dr Anand Natarajan - Precision Brain, Spine & Pain Centre10 novembro 2024
Dr Anand Natarajan - Precision Brain, Spine & Pain Centre10 novembro 2024 -
 Pin de Tiah Heninger em print outs Roupas de boneca de papel, Modelo de boneca de papel, Bonequinhas kawaii10 novembro 2024
Pin de Tiah Heninger em print outs Roupas de boneca de papel, Modelo de boneca de papel, Bonequinhas kawaii10 novembro 2024 -
 Dragon Ball Z - Shin Budokai 2 ROM - PSP Download - Emulator Games10 novembro 2024
Dragon Ball Z - Shin Budokai 2 ROM - PSP Download - Emulator Games10 novembro 2024 -
Conselho Nacional de Justiça (CNJ) - Se o documento estudantil10 novembro 2024
-
 uwu Meaning & Origin Slang by10 novembro 2024
uwu Meaning & Origin Slang by10 novembro 2024 -
A Maldição de Bridge Hollow: Halloween ganha vida no trailer da10 novembro 2024
-
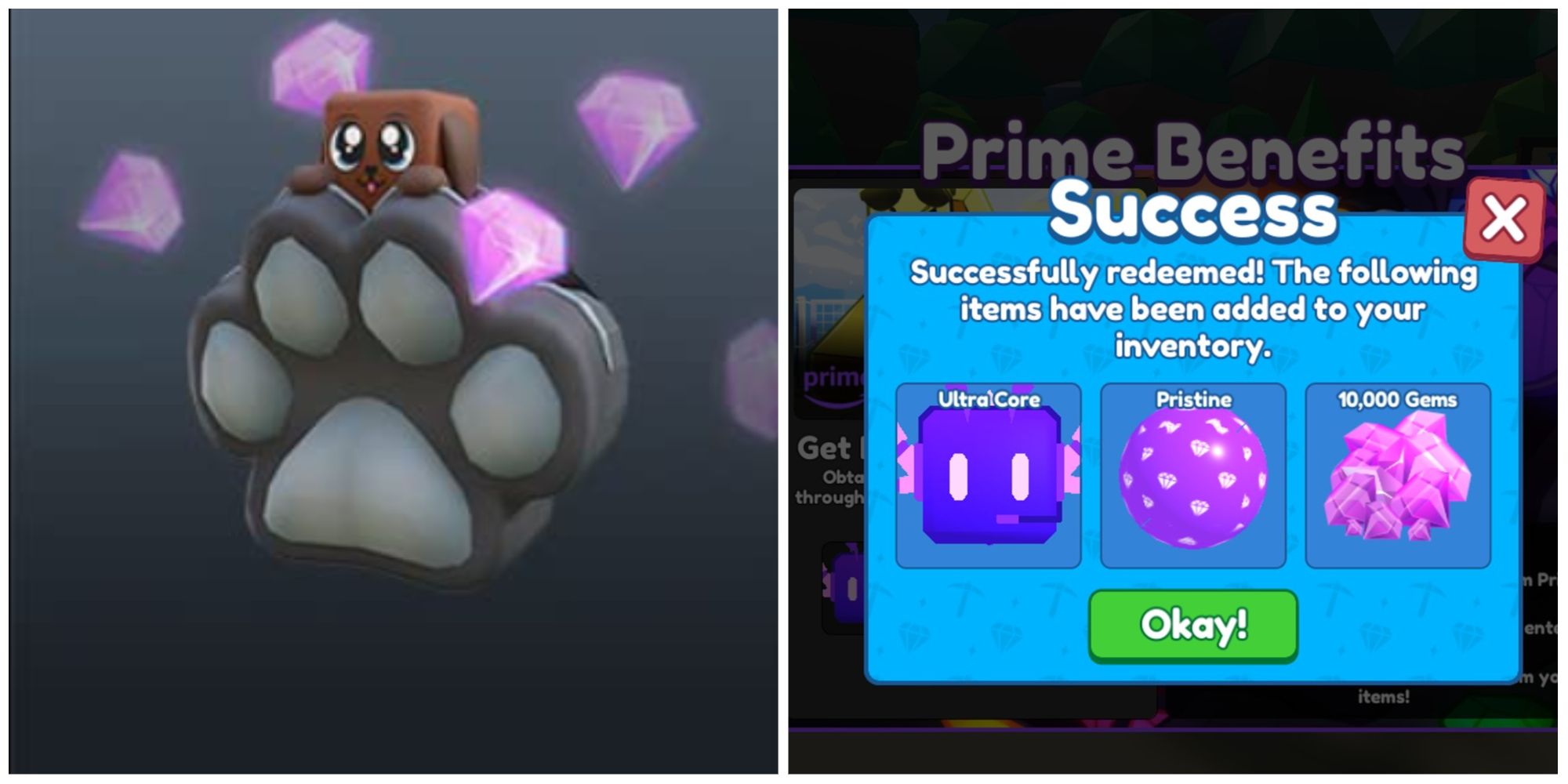 How To Get The Prime Backpack In Mining Simulator 210 novembro 2024
How To Get The Prime Backpack In Mining Simulator 210 novembro 2024 -
José Mazer - Marketing Staff - Palusa10 novembro 2024
-
 Hazlo 🔫 : r/MAAU10 novembro 2024
Hazlo 🔫 : r/MAAU10 novembro 2024




