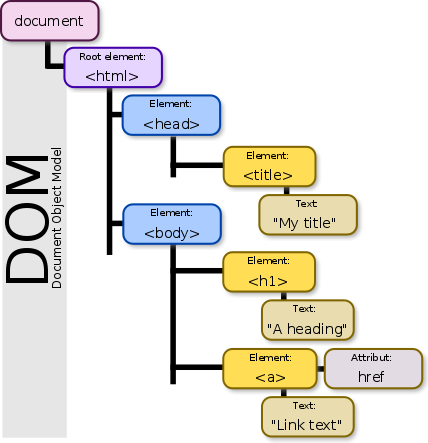
PDF] Figure 1: Architecture of XSS attack Injection of code into
Por um escritor misterioso
Last updated 22 dezembro 2024
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://d3i71xaburhd42.cloudfront.net/c976c25cbfcac95b7f9ca9b5783a731a75426605/1-Figure1-1.png)
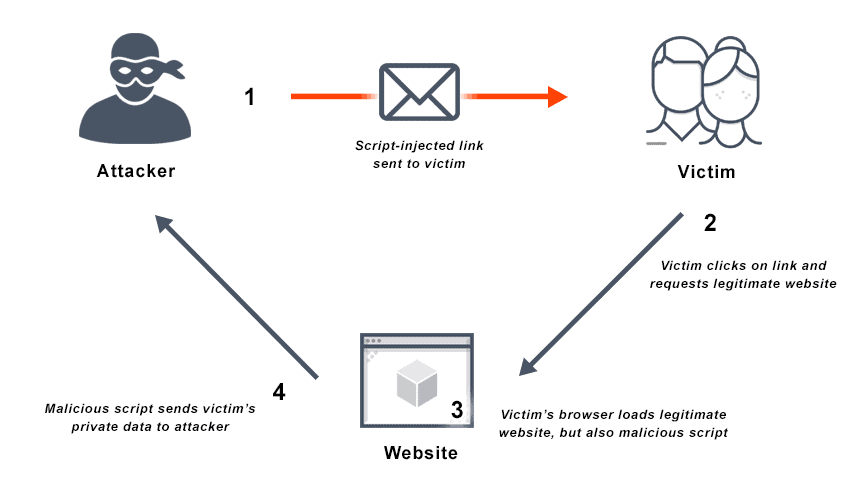
This work aims at developing a solution in web applications undergo rigorous testing by being a target to the engine and consequently finding flaws embedded within them. 549 Published By: Blue Eyes Intelligence Engineering & Sciences Publication Retrieval Number: F2318037619/19©BEIESP Abstract: Web applications actively replace native applications due to their flexible nature. They can be easily deployed and scaled, which require constant interaction with the user machine for software updates. Widespread use of cloud computing [10] has resulted in favoring web applications for easy deployment and scalability. Today the movement of software applications to the web has resulted to web application vulnerabilities [1]. Instead of targeting multiple operating systems or platforms, attackers can focus on exploiting web applications for compromising sensitive information. Web browsers act as the interface between the user and the web and are crucial for user security. The client-side attacks can result in the compromise of credentials and identity theft. In this paper, totally three models are developed namely Injection of code into un-sanitized parameters, Browser exploitation techniques and Manipulation of application registries which serve as the basis for exploiting and subsequently preventing cross-site scripting vulnerabilities [3]. By using these models as a foundation, the attacks are minimized in a large scale. In this work the results shows that, for the random sample of attack vectors 4, 2, 9, the vulnerability score is 0, which is considered to be minimum and forth random sample of attack vectors 2, 5, 7 the vulnerability score is 89.12 which is considered to be maximum. This work aims at developing a solution in web applications undergo rigorous testing by being a target to the engine and consequently finding flaws embedded within them.
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://blog.netwrix.com/wp-content/uploads/2018/05/CA_cyberattacks_xssattack.png)
The 12 Most Common Types of Cybersecurity Attacks Today
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.researchgate.net/profile/Jyoti-Snehi/publication/324986959/figure/fig4/AS:623655188955138@1525702392241/figure-fig4_Q320.jpg)
PDF) Web Client and Web Server approaches to Prevent XSS Attacks
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://d3i71xaburhd42.cloudfront.net/c976c25cbfcac95b7f9ca9b5783a731a75426605/5-Table1-1.png)
PDF] Figure 1: Architecture of XSS attack Injection of code into un-sanitized parameters, Browser exploitation techniques and Manipulation of application registries which serve as the basis for exploiting and subsequently preventing cross-site
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.feistyduck.com/library/apache-security/online/figs/apcs_1001.png)
Apache Security: Chapter 10. Web Application Security
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://media.springernature.com/m685/springer-static/image/art%3A10.1186%2Fs40537-022-00678-0/MediaObjects/40537_2022_678_Fig3_HTML.png)
Detection and prevention of SQLI attacks and developing compressive framework using machine learning and hybrid techniques, Journal of Big Data
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://0.academia-photos.com/attachment_thumbnails/103494208/mini_magick20230618-1-ey93cr.png?1687080423)
PDF) Analysis of XSS attack Mitigation techniques based on Platforms and Browsers
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://onlinelibrary.wiley.com/cms/asset/9c25acb9-e1ee-4e73-8040-de6556250c78/ett4872-fig-0001-m.jpg)
HTTP header based phishing attack detection using machine learning - Shukla - Transactions on Emerging Telecommunications Technologies - Wiley Online Library
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.researchgate.net/profile/S-Pandian/publication/281601290/figure/fig2/AS:505849417342976@1497615307352/Architecture-of-Exploiting-the-Persistent-XSS-Attack-232-Non-persistent-XSS-Attack_Q320.jpg)
PDF) A Survey on Detection and Prevention of Cross-Site Scripting Attack
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.tandfonline.com/cms/asset/43a86af6-61aa-4838-96b0-84f02e2ef77f/wasr_a_1735283_f0003_c.jpg)
Full article: Case Study: Extenuation of XSS Attacks through Various Detecting and Defending Techniques
Recomendado para você
-
 XSS Injection Campaign Exploits WordPress AMP Plugin22 dezembro 2024
XSS Injection Campaign Exploits WordPress AMP Plugin22 dezembro 2024 -
 What is Cross Site Scripting? Definition & FAQs22 dezembro 2024
What is Cross Site Scripting? Definition & FAQs22 dezembro 2024 -
 Cross site scripting (XSS) attack - Types and Examples22 dezembro 2024
Cross site scripting (XSS) attack - Types and Examples22 dezembro 2024 -
 SQL injection and XSS: what white hat hackers know about trusting22 dezembro 2024
SQL injection and XSS: what white hat hackers know about trusting22 dezembro 2024 -
 What is Cross-Site Scripting? XSS Cheat Sheet22 dezembro 2024
What is Cross-Site Scripting? XSS Cheat Sheet22 dezembro 2024 -
 Cross-Site Scripting: XSS Injection » Hacking Lethani22 dezembro 2024
Cross-Site Scripting: XSS Injection » Hacking Lethani22 dezembro 2024 -
Building Secure Websites: Safeguarding User Data from Cross-Site22 dezembro 2024
-
 SQL Injection attack using the XSS22 dezembro 2024
SQL Injection attack using the XSS22 dezembro 2024 -
 Vulnérabilité XSS, ou injection de code indirecte à distance22 dezembro 2024
Vulnérabilité XSS, ou injection de code indirecte à distance22 dezembro 2024 -
 DOM-based XSS - The 3 Sinks - Brute XSS22 dezembro 2024
DOM-based XSS - The 3 Sinks - Brute XSS22 dezembro 2024
você pode gostar
-
/i621670.jpeg) t.ctcdn.com.br/dzY2_MJN18QIdzHRRVDaJE9_TyI=/1024x022 dezembro 2024
t.ctcdn.com.br/dzY2_MJN18QIdzHRRVDaJE9_TyI=/1024x022 dezembro 2024 -
 Ender Dragon Minecraft Skin22 dezembro 2024
Ender Dragon Minecraft Skin22 dezembro 2024 -
 How to get more characters in Roblox All Star Tower Defense? - Pro Game Guides22 dezembro 2024
How to get more characters in Roblox All Star Tower Defense? - Pro Game Guides22 dezembro 2024 -
 Foto de Charlie Day - Quero Matar Meu Chefe : Fotos Charlie Day, Seth Gordon, Jason Bateman - Foto 67 de 82 - AdoroCinema22 dezembro 2024
Foto de Charlie Day - Quero Matar Meu Chefe : Fotos Charlie Day, Seth Gordon, Jason Bateman - Foto 67 de 82 - AdoroCinema22 dezembro 2024 -
 30 Creative Emo Hairstyles and Haircuts for Girls in 202322 dezembro 2024
30 Creative Emo Hairstyles and Haircuts for Girls in 202322 dezembro 2024 -
 How to Verify Channel In Studio22 dezembro 2024
How to Verify Channel In Studio22 dezembro 2024 -
 DENNY ROSE Made in ITALY Pants Size M and Top Size S NEW with Tags22 dezembro 2024
DENNY ROSE Made in ITALY Pants Size M and Top Size S NEW with Tags22 dezembro 2024 -
role underground|Pesquisa do TikTok22 dezembro 2024
-
 MTGNexus - Brainiac, World Ender22 dezembro 2024
MTGNexus - Brainiac, World Ender22 dezembro 2024 -
 AniPlaylist KONOSUBA God's blessing on this wonderful world! Legend of Crimson Ending 2 on Spotify & Apple Music22 dezembro 2024
AniPlaylist KONOSUBA God's blessing on this wonderful world! Legend of Crimson Ending 2 on Spotify & Apple Music22 dezembro 2024

