Malware analysis Malicious activity
Por um escritor misterioso
Last updated 19 setembro 2024

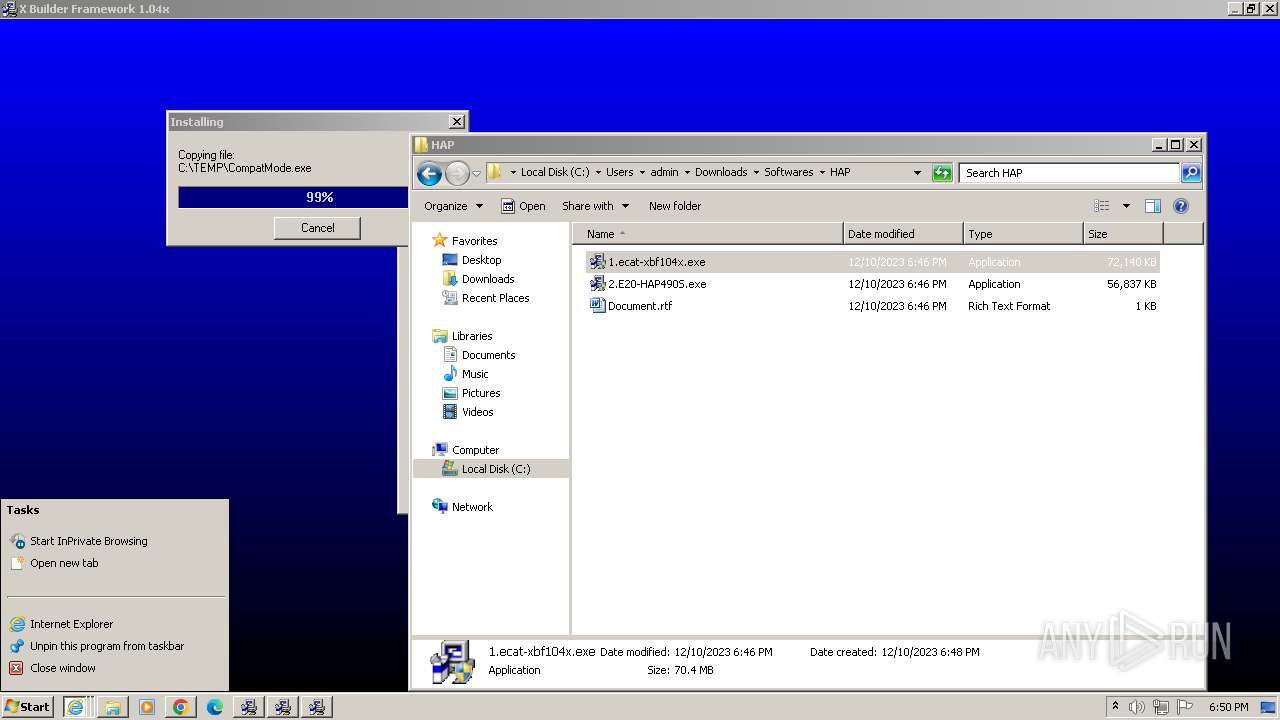
Malware analysis CQChallenge5.zip Malicious activity

Building A Simple Malware Analysis Pipeline In The Homelab Pt - 1 · Arch Cloud Labs

Malware Analysis Benefits Incident Response

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

TryHackMe Cyber Security Exercises and Labs

Unveiling activities of Tropic Trooper 2023 deep analysis of Xiangoop Loader and EntryShell payload

Interactive Online Malware Sandbox
GitHub - mesquidar/ForensicsTools: A list of free and open forensics analysis tools and other resources
Malware analysis Malicious activity

Malware Analysis Framework v1.0

The latest malicious activity and how to deal with it

Malware analysis cd53fba6ddd4ae4ef7a5747c6003236c85791477854cc1b7ce00e0f8ee7677d9 Malicious activity

Top 10 Types of Information Security Threats for IT Teams
Recomendado para você
-
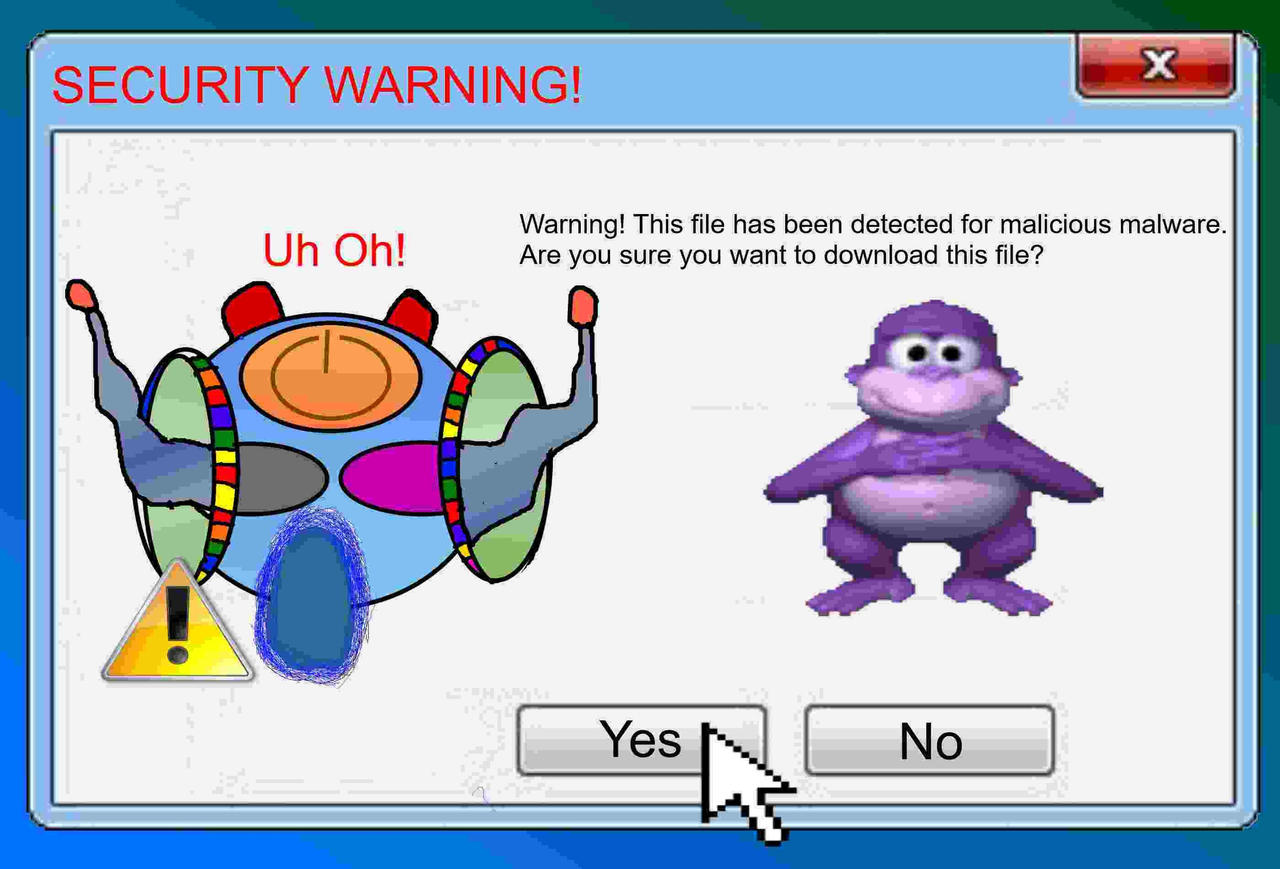 Originally Titled: Bonzi Buddy virus by Andnrok on DeviantArt19 setembro 2024
Originally Titled: Bonzi Buddy virus by Andnrok on DeviantArt19 setembro 2024 -
Steam Workshop::Bonzi Buddy19 setembro 2024
-
![Bonzi Buddy (Creditos a Axl Brett) - Download Free 3D model by Bendy y Boris Gamers (@Bendylianoram123) [855b9a7]](https://media.sketchfab.com/models/855b9a781cc04b54b37ccd3e5fde04f3/thumbnails/31db1d0f427a455b83137c287fba564e/7b58e78ccb6e4ccd9363f06a16c725e3.jpeg) Bonzi Buddy (Creditos a Axl Brett) - Download Free 3D model by Bendy y Boris Gamers (@Bendylianoram123) [855b9a7]19 setembro 2024
Bonzi Buddy (Creditos a Axl Brett) - Download Free 3D model by Bendy y Boris Gamers (@Bendylianoram123) [855b9a7]19 setembro 2024 -
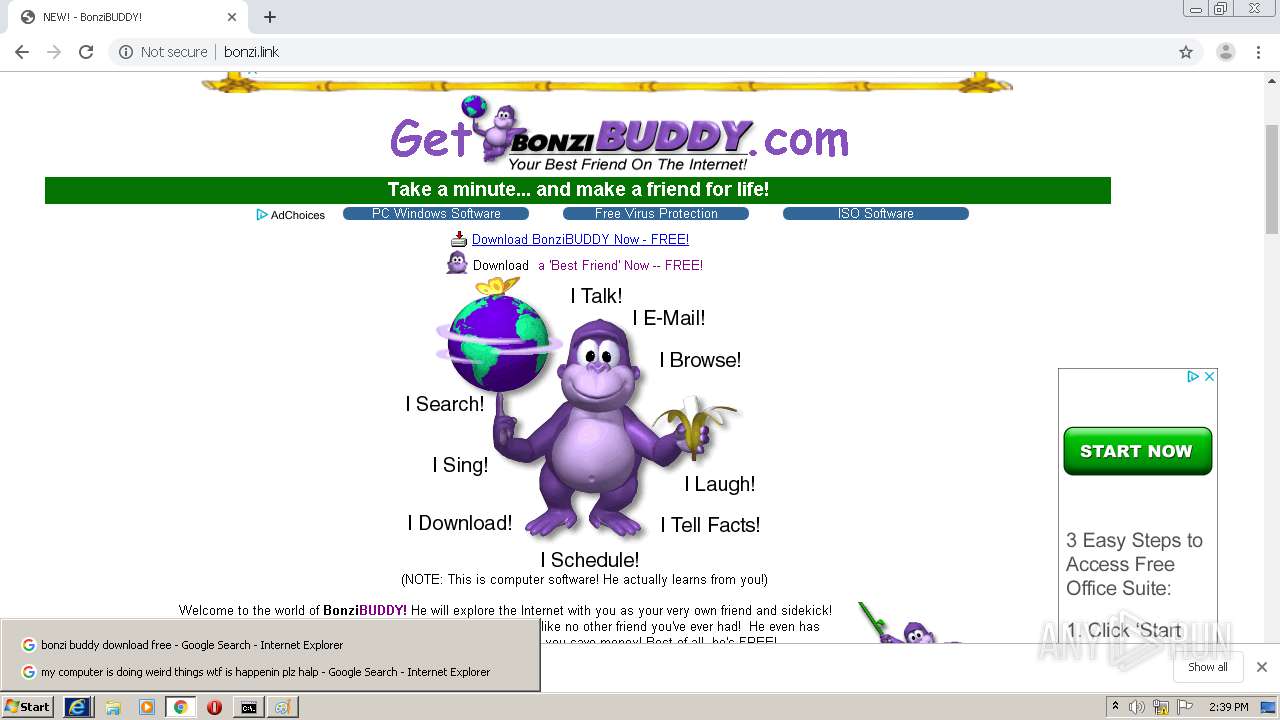
 NEW! - BonziBUDDY!19 setembro 2024
NEW! - BonziBUDDY!19 setembro 2024 -
 BONZIBUDDY bonzisoftware19 setembro 2024
BONZIBUDDY bonzisoftware19 setembro 2024 -
 The Original BonziBUDDY : Bonzi Software : Free Download, Borrow, and Streaming : Internet Archive19 setembro 2024
The Original BonziBUDDY : Bonzi Software : Free Download, Borrow, and Streaming : Internet Archive19 setembro 2024 -
BonziBuddy Theme Plaza19 setembro 2024
-
 BonziBuddy Download IOS – App valley19 setembro 2024
BonziBuddy Download IOS – App valley19 setembro 2024 -
![Bonzi Buddy - 3D model by Bendy y Boris Gamers (@Bendylianoram123) [0be0448]](https://media.sketchfab.com/models/0be04483f7654e1ab3cd92414a5a0f49/thumbnails/dc20af52f8804292b9d967b667759f56/854689505b514b31bbcf5bd5b55a4146.jpeg) Bonzi Buddy - 3D model by Bendy y Boris Gamers (@Bendylianoram123) [0be0448]19 setembro 2024
Bonzi Buddy - 3D model by Bendy y Boris Gamers (@Bendylianoram123) [0be0448]19 setembro 2024 -
Steam Workshop::[DRGBase] Bonzi Buddy19 setembro 2024
você pode gostar
-
 How To Get Shiny Shadow Lugia In Pokemon GO19 setembro 2024
How To Get Shiny Shadow Lugia In Pokemon GO19 setembro 2024 -
 Creeper Minecraft Svg/ Creeper Cricut File/ Creeper Layered19 setembro 2024
Creeper Minecraft Svg/ Creeper Cricut File/ Creeper Layered19 setembro 2024 -
 Splinter Cell Conviction 25 artwork by wert23 on DeviantArt19 setembro 2024
Splinter Cell Conviction 25 artwork by wert23 on DeviantArt19 setembro 2024 -
IT MOVES] Noob Buddy Head - Roblox19 setembro 2024
-
 How to apply a livery in Gran Turismo 719 setembro 2024
How to apply a livery in Gran Turismo 719 setembro 2024 -
 Buffet de Comidas Juninas, festas juninas, barraquinhas comidas juninas19 setembro 2024
Buffet de Comidas Juninas, festas juninas, barraquinhas comidas juninas19 setembro 2024 -
 weirdcore #freetoedit Dreamcore weirdcore, Weirdcore aesthetic, Dreamcore aesthetic19 setembro 2024
weirdcore #freetoedit Dreamcore weirdcore, Weirdcore aesthetic, Dreamcore aesthetic19 setembro 2024 -
 Bicicleta Ergométrica Vertical Ronaldinho para até 120kg - dream19 setembro 2024
Bicicleta Ergométrica Vertical Ronaldinho para até 120kg - dream19 setembro 2024 -
 Sega vs. Nintendo: Relembre a guerra dos consoles dos anos 9019 setembro 2024
Sega vs. Nintendo: Relembre a guerra dos consoles dos anos 9019 setembro 2024 -
 Brincadeiras para crianças na praia: veja 5 ideias - Blog da Alice19 setembro 2024
Brincadeiras para crianças na praia: veja 5 ideias - Blog da Alice19 setembro 2024

![Steam Workshop::[DRGBase] Bonzi Buddy](https://steamuserimages-a.akamaihd.net/ugc/1777256672045467787/9A76EE1DFE107A4F8D1A13A460287F7E8DE8AA5C/?imw=637&imh=358&ima=fit&impolicy=Letterbox&imcolor=%23000000&letterbox=true)