Malware analysis Malicious activity
Por um escritor misterioso
Last updated 31 dezembro 2024

Dynamic malware analysis [34]

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

Malware Analysis: Steps & Examples - CrowdStrike

Free Cybersecurity Training and Career Development
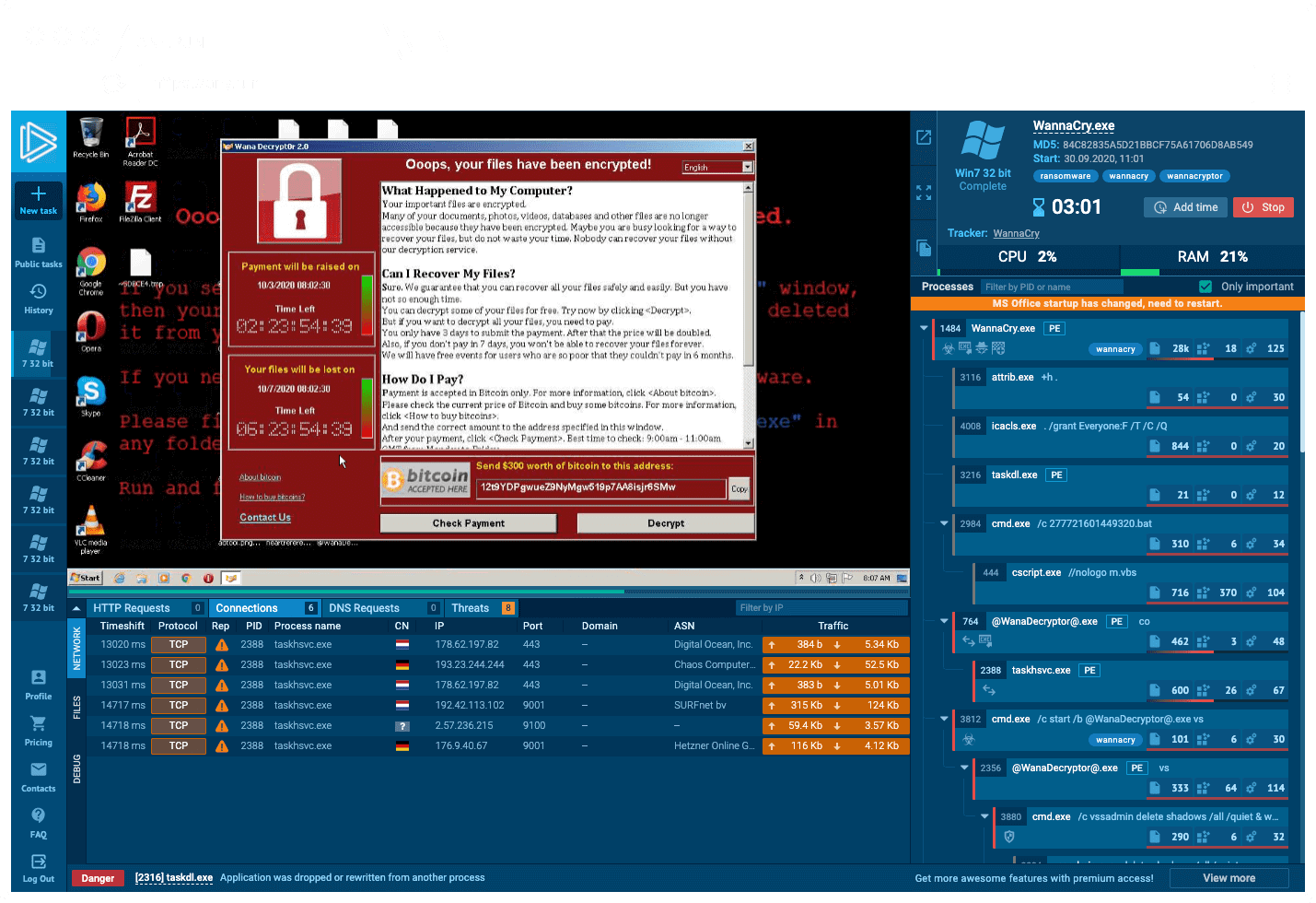
Interactive Online Malware Sandbox

Malware Analysis: Steps & Examples - CrowdStrike

Robust Malware Detection Models: Learning From Adversarial Attacks and Defenses - Forensic Focus

Detail procedure of malware analysis

Malware analysis tt.7z Malicious activity

TryHackMe Hacktivities

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen
Recomendado para você
-
 Jōnin, Narutopedia31 dezembro 2024
Jōnin, Narutopedia31 dezembro 2024 -
 The Orange Sensei - Chapter 1: Naruto the Jounin-sensei - Page 3 - Wattpad31 dezembro 2024
The Orange Sensei - Chapter 1: Naruto the Jounin-sensei - Page 3 - Wattpad31 dezembro 2024 -
![NARUTO SHIPPUDEN Grandista HATAKE KAKASHI [MANGA DIMENSIONS]](https://www.littlebuddytoys.com/wp-content/uploads/2022/03/18663_1.jpg) NARUTO SHIPPUDEN Grandista HATAKE KAKASHI [MANGA DIMENSIONS]31 dezembro 2024
NARUTO SHIPPUDEN Grandista HATAKE KAKASHI [MANGA DIMENSIONS]31 dezembro 2024 -
 Kakashi Hatake, the Jonin in Charge, NARUTO: SHIPPUDEN31 dezembro 2024
Kakashi Hatake, the Jonin in Charge, NARUTO: SHIPPUDEN31 dezembro 2024 -
Clan Jounin gakure31 dezembro 2024
-
 Finally a clash! Jōnin vs. Genin!! Indiscriminate Grand Melee Tournament Meeting!!, Narutopedia31 dezembro 2024
Finally a clash! Jōnin vs. Genin!! Indiscriminate Grand Melee Tournament Meeting!!, Narutopedia31 dezembro 2024 -
 Naruto - Imagem oficial mostra o personagem com o uniforme dos Jounin!31 dezembro 2024
Naruto - Imagem oficial mostra o personagem com o uniforme dos Jounin!31 dezembro 2024 -
 Kushina Uzumaki - Ninja Saga, The best Ninja Saga website.31 dezembro 2024
Kushina Uzumaki - Ninja Saga, The best Ninja Saga website.31 dezembro 2024 -
 Team 8 on NarutoLoverz - DeviantArt31 dezembro 2024
Team 8 on NarutoLoverz - DeviantArt31 dezembro 2024 -
Can you visibly distinguish the difference of ranking of Shinobi in Naruto? Age normally makes it obvious they're not G, but I think it would be cool if there was a visible31 dezembro 2024
você pode gostar
-
 Microsoft Flight Simulator on Xbox is a technical marvel and31 dezembro 2024
Microsoft Flight Simulator on Xbox is a technical marvel and31 dezembro 2024 -
 Premium Vector Grim reaper death stoner skull halloween hand drawn cartoon sticker icon concept illustration31 dezembro 2024
Premium Vector Grim reaper death stoner skull halloween hand drawn cartoon sticker icon concept illustration31 dezembro 2024 -
/i.s3.glbimg.com/v1/AUTH_08fbf48bc0524877943fe86e43087e7a/internal_photos/bs/2021/a/E/Gd1YCyT7exSABinK2LSA/2013-10-15-gta.png) Dicas de GTA 5 para iniciantes: veja 10 truques essenciais para jogar31 dezembro 2024
Dicas de GTA 5 para iniciantes: veja 10 truques essenciais para jogar31 dezembro 2024 -
 Quem é o irmão gêmeo de The Rock?31 dezembro 2024
Quem é o irmão gêmeo de The Rock?31 dezembro 2024 -
 Project Kid Hack - Teaching Kids Security through Gaming at31 dezembro 2024
Project Kid Hack - Teaching Kids Security through Gaming at31 dezembro 2024 -
 Escultura torre jogo de xadrez decorativa metal E marmore em Promoção na Americanas31 dezembro 2024
Escultura torre jogo de xadrez decorativa metal E marmore em Promoção na Americanas31 dezembro 2024 -
 Festival de Cannes começa com Johnny Depp como Luís XV31 dezembro 2024
Festival de Cannes começa com Johnny Depp como Luís XV31 dezembro 2024 -
Epic Games loses again on restoring Fortnite to Apple Store31 dezembro 2024
-
 MALACASA, Series Felisa, 36-Piece Porcelain Dinnerware Set, Red Stripes Ivory White Dinner Set, Service for 1231 dezembro 2024
MALACASA, Series Felisa, 36-Piece Porcelain Dinnerware Set, Red Stripes Ivory White Dinner Set, Service for 1231 dezembro 2024 -
 Star Wars: Episode I - The Phantom Menace Movie Review for Parents31 dezembro 2024
Star Wars: Episode I - The Phantom Menace Movie Review for Parents31 dezembro 2024

