Malware analysis Malicious activity
Por um escritor misterioso
Last updated 10 novembro 2024

How to Do Malware Analysis?

What to Include in a Malware Analysis Report

Detail procedure of malware analysis

MetaDefender Cloud Advanced threat prevention and detection

FBI, CISA, MS-ISAC release cybersecurity advisory on emerging Rhysida ransomware targeting critical sectors - Industrial Cyber
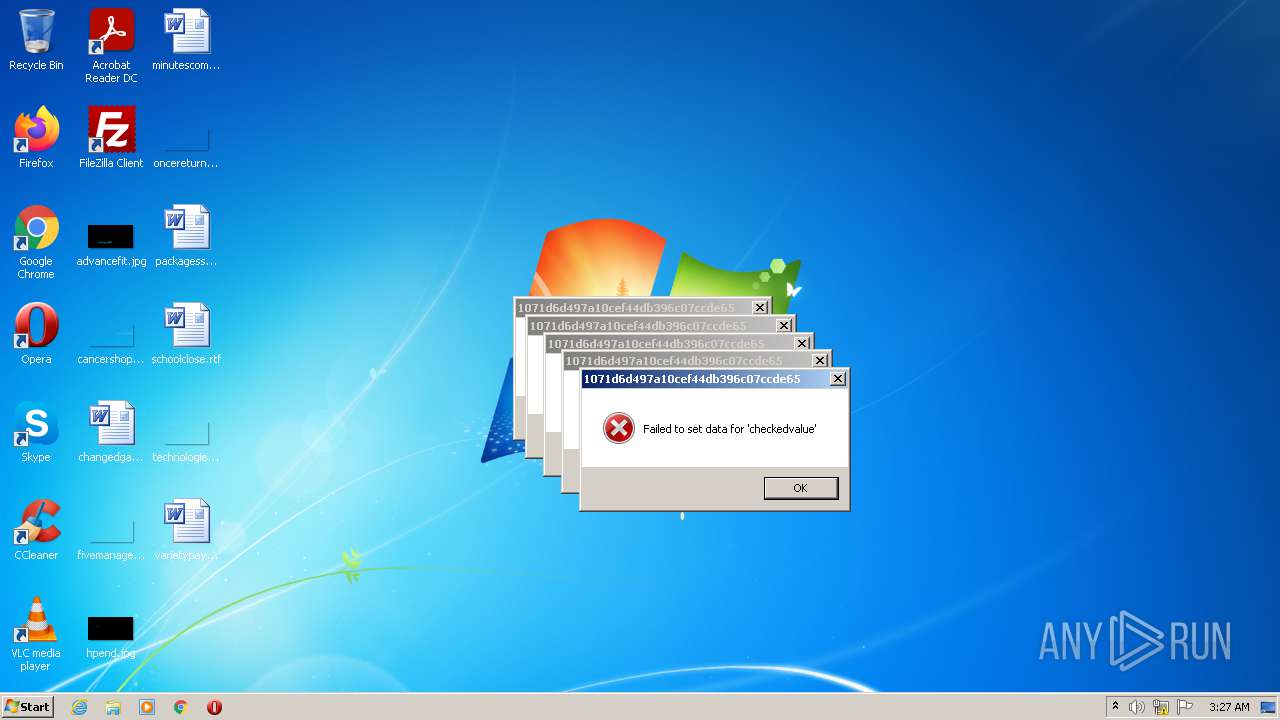
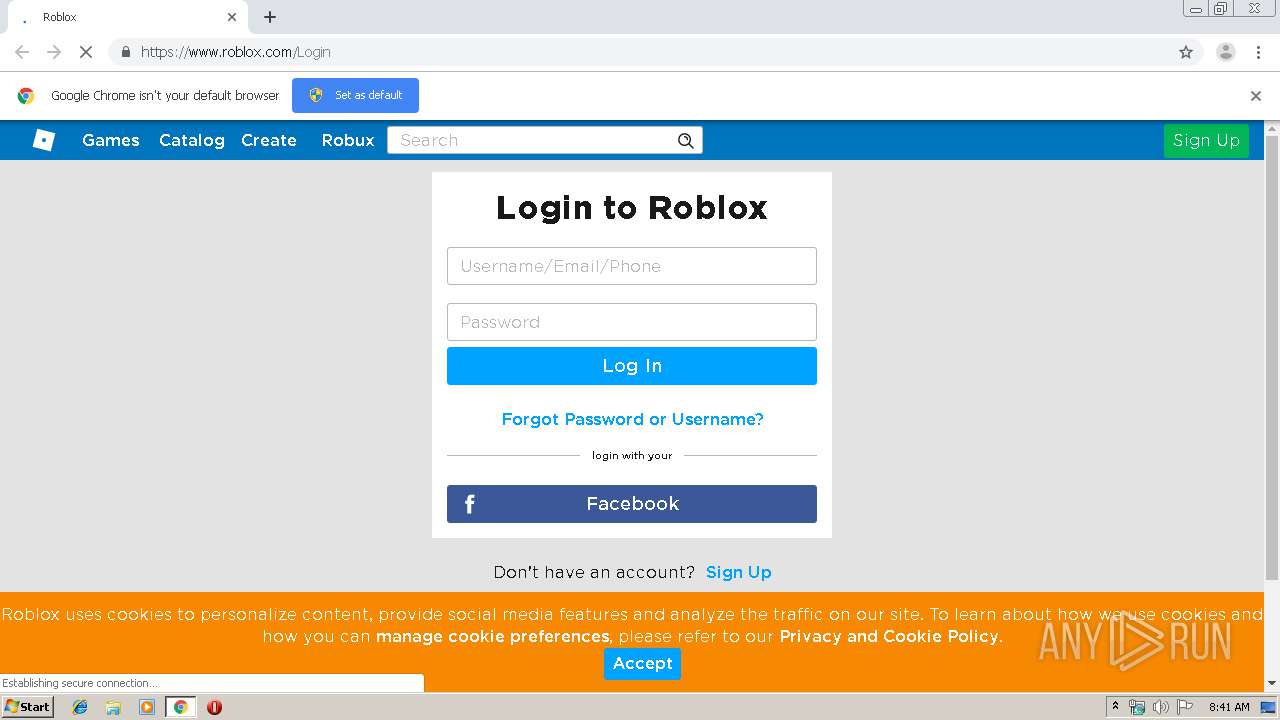
Malware analysis 1071d6d497a10cef44db396c07ccde65 Malicious activity

Dynamic Malware Analysis in the Modern Era—A State of the Art Survey
GitHub - mesquidar/ForensicsTools: A list of free and open forensics analysis tools and other resources

Top 10 Types of Information Security Threats for IT Teams
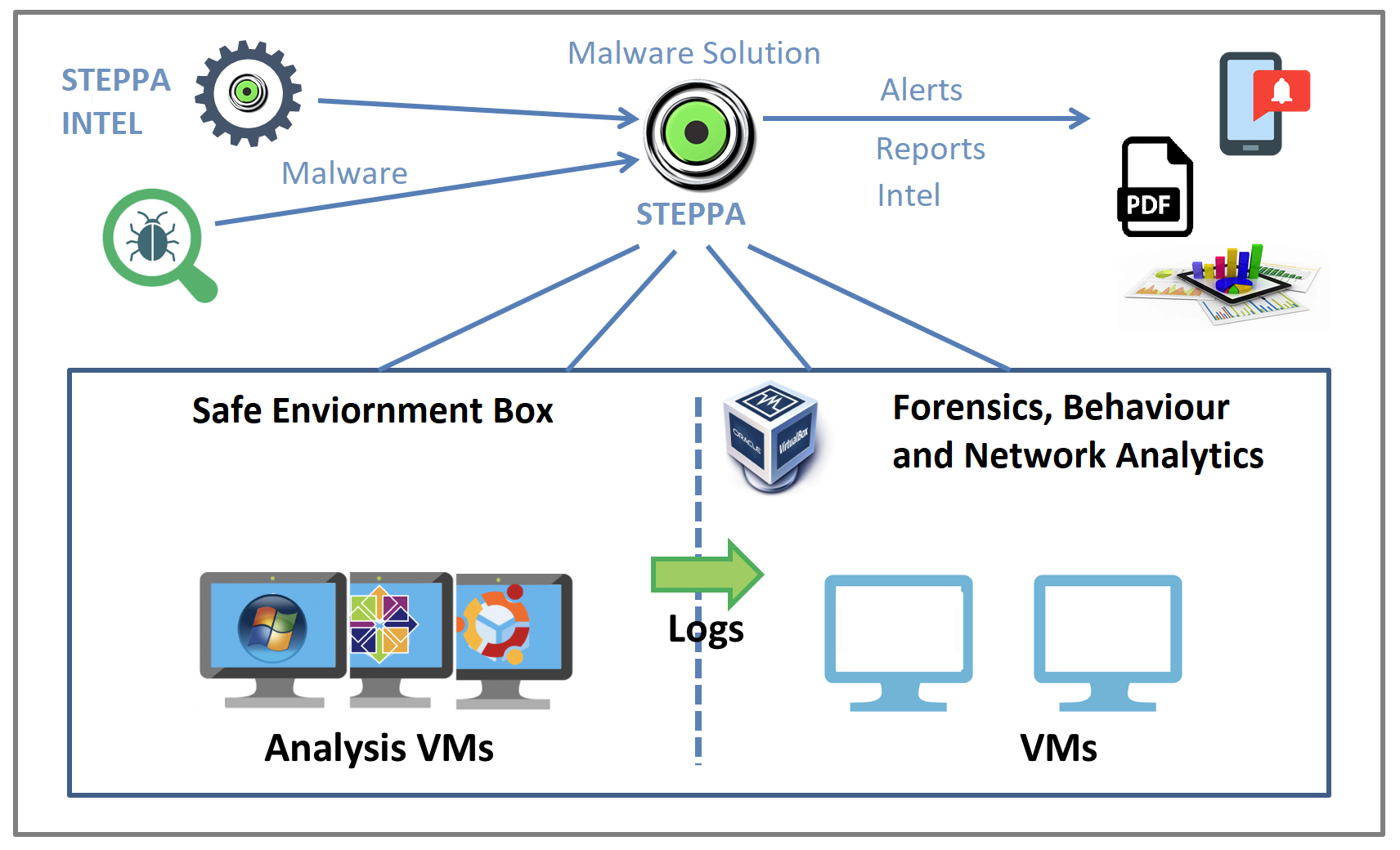
Malware Analysis Solution: Analyze, Detect, and Protect

Unveiling activities of Tropic Trooper 2023 deep analysis of Xiangoop Loader and EntryShell payload
Lab 6-1 Solutions - Practical Malware Analysis [Book]
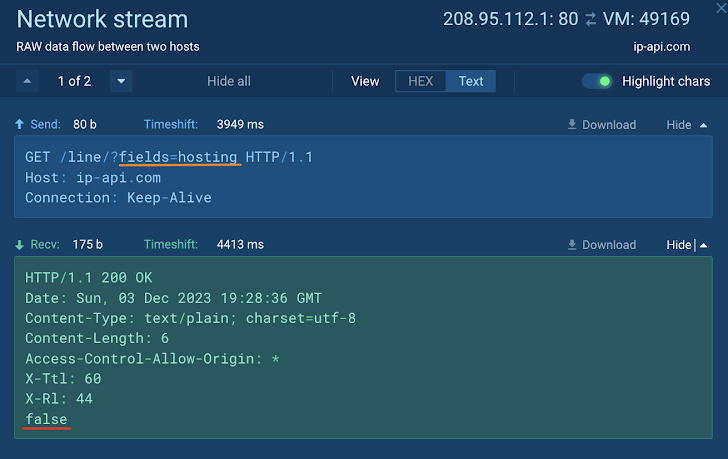
How to Analyze Malware's Network Traffic in A Sandbox

Static malware analysis workflow.
Malware analysis index.html Malicious activity
Recomendado para você
-
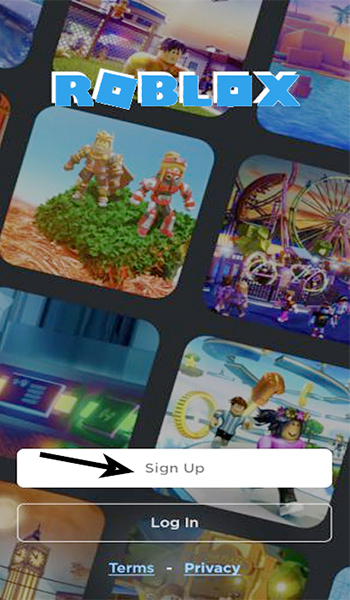 How To Create An Account on Roblox?10 novembro 2024
How To Create An Account on Roblox?10 novembro 2024 -
 Playing on Roblox Documentation - Roblox Creator Hub10 novembro 2024
Playing on Roblox Documentation - Roblox Creator Hub10 novembro 2024 -
 How do you Login to roblox with your facebook10 novembro 2024
How do you Login to roblox with your facebook10 novembro 2024 -
 How To Add Facebook Link To Roblox Profile10 novembro 2024
How To Add Facebook Link To Roblox Profile10 novembro 2024 -
 Cant Login To Your ROBLOX ACCOUNT! (ROBLOX ERROR DOWN)10 novembro 2024
Cant Login To Your ROBLOX ACCOUNT! (ROBLOX ERROR DOWN)10 novembro 2024 -
 How to Change your Name on Roblox Account in 2 Minutes?10 novembro 2024
How to Change your Name on Roblox Account in 2 Minutes?10 novembro 2024 -
 Is Roblox safe for children - see parent's guide10 novembro 2024
Is Roblox safe for children - see parent's guide10 novembro 2024 -
 How to Sign Up for an Account on Roblox: 6 Steps (with Pictures)10 novembro 2024
How to Sign Up for an Account on Roblox: 6 Steps (with Pictures)10 novembro 2024 -
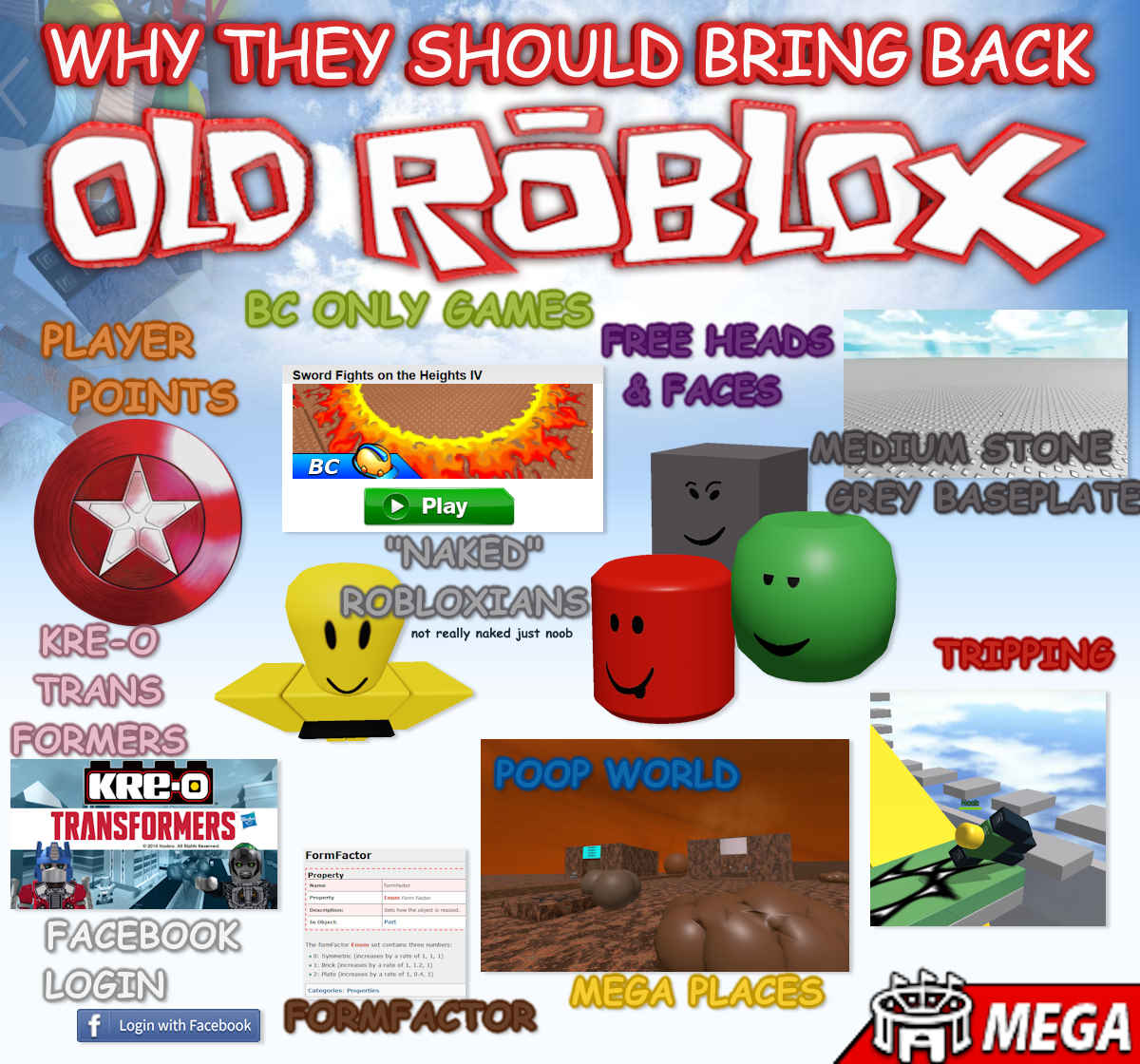 ChadTheCreator on X: I repeat again: Most of these things sucked10 novembro 2024
ChadTheCreator on X: I repeat again: Most of these things sucked10 novembro 2024 -
 The Roblox 'oof' sound is dead. Why it was removed and how it's going so far10 novembro 2024
The Roblox 'oof' sound is dead. Why it was removed and how it's going so far10 novembro 2024
você pode gostar
-
 shu kurenai Maëlys LG - Illustrations ART street10 novembro 2024
shu kurenai Maëlys LG - Illustrations ART street10 novembro 2024 -
 Vetores de Cavalo Preto E Branco Desenho e mais imagens de Cavalo - Família do cavalo - Cavalo - Família do cavalo, Clip Art, Colorindo - iStock10 novembro 2024
Vetores de Cavalo Preto E Branco Desenho e mais imagens de Cavalo - Família do cavalo - Cavalo - Família do cavalo, Clip Art, Colorindo - iStock10 novembro 2024 -
 Minecraft gratuito nas escolas da Irlanda do Norte10 novembro 2024
Minecraft gratuito nas escolas da Irlanda do Norte10 novembro 2024 -
 The ridiculous Naruto picture thread - Page 118 - AnimeSuki Forum10 novembro 2024
The ridiculous Naruto picture thread - Page 118 - AnimeSuki Forum10 novembro 2024 -
 FNF vs Tails.EXE V2 FNF mod game play online, pc download10 novembro 2024
FNF vs Tails.EXE V2 FNF mod game play online, pc download10 novembro 2024 -
) Quebra-Cabeça Puzzle 60 Peças - Frozen II - Anna - Toyster10 novembro 2024
Quebra-Cabeça Puzzle 60 Peças - Frozen II - Anna - Toyster10 novembro 2024 -
 Southeast Native Wildflower Seed Mix10 novembro 2024
Southeast Native Wildflower Seed Mix10 novembro 2024 -
 Love Drama Club Baby Pink & White Design T-Shirt10 novembro 2024
Love Drama Club Baby Pink & White Design T-Shirt10 novembro 2024 -
 Garotas esportivas passando bola de futebol em campo verde. duas meninas em roupas esportivas jogando futebol juntos, correndo rápido e profissionalmente chutando bola. estilo de vida saudável e conceito de futebol feminino10 novembro 2024
Garotas esportivas passando bola de futebol em campo verde. duas meninas em roupas esportivas jogando futebol juntos, correndo rápido e profissionalmente chutando bola. estilo de vida saudável e conceito de futebol feminino10 novembro 2024 -
Serena's Soulfood Catering10 novembro 2024
