Malware analysis Malicious activity
Por um escritor misterioso
Last updated 20 setembro 2024

Building A Simple Malware Analysis Pipeline In The Homelab Pt - 1 · Arch Cloud Labs

Detail procedure of malware analysis

Cybersecurity Search Engine

How to Remove Windows Defender Security Warning Scam

FBI, CISA, MS-ISAC release cybersecurity advisory on emerging Rhysida ransomware targeting critical sectors - Industrial Cyber

Free Cybersecurity Training and Career Development

Remediation and Malware Detection Overview

Top 10 Types of Information Security Threats for IT Teams
Malware analysis file Malicious activity
Lab 6-1 Solutions - Practical Malware Analysis [Book]

Malware leveraging public infrastructure like GitHub on the rise - Security Boulevard

Malware analysis AIO_4.9.8__ed.rar Malicious activity
Recomendado para você
-
 What is Cookie Logging? – CrowdStrike20 setembro 2024
What is Cookie Logging? – CrowdStrike20 setembro 2024 -
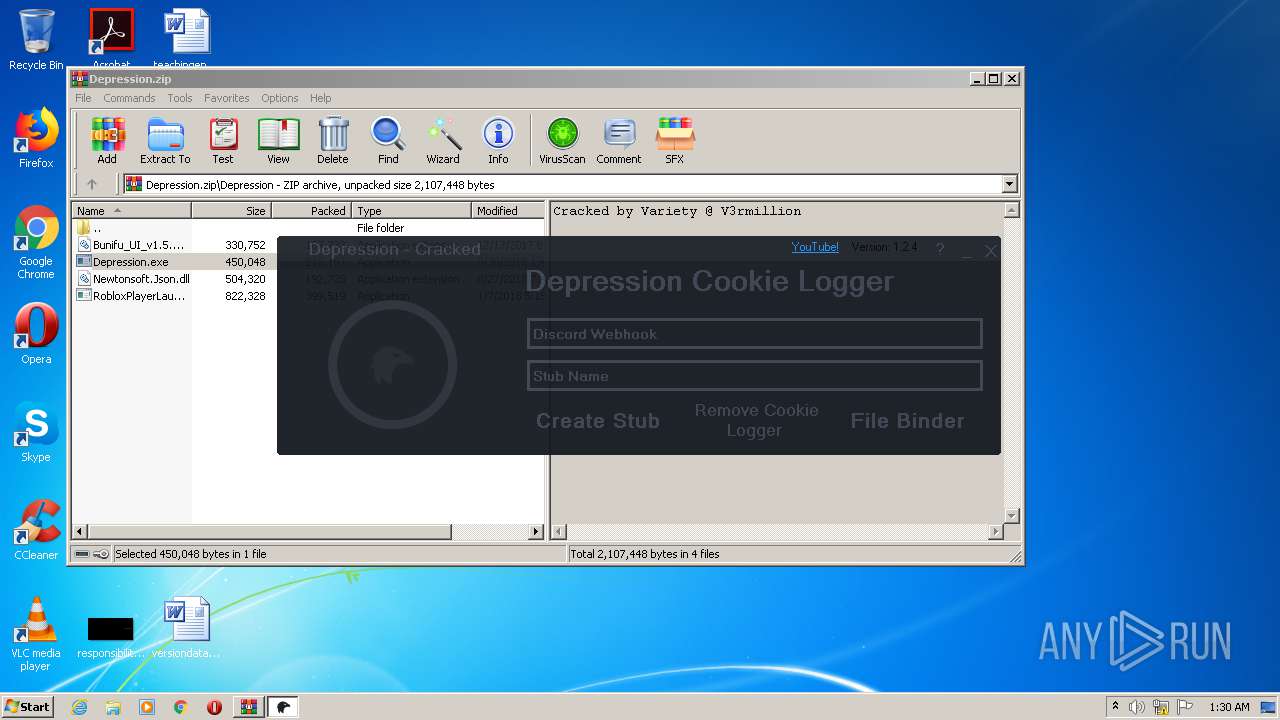 Malware analysis Depression.zip Malicious activity20 setembro 2024
Malware analysis Depression.zip Malicious activity20 setembro 2024 -
 ROBLOSECURITY, Roblox Wiki20 setembro 2024
ROBLOSECURITY, Roblox Wiki20 setembro 2024 -
Configuring LifeTime authentication - OutSystems 11 Documentation20 setembro 2024
-
Fake Ip Grabber Script20 setembro 2024
-
 MetroLog.Maui: logging taylor-made for Maui20 setembro 2024
MetroLog.Maui: logging taylor-made for Maui20 setembro 2024 -
Roblox API CSRF token not working only on railway - Railway20 setembro 2024
-
 USD Stage Editor Quick Start in Unreal Engine20 setembro 2024
USD Stage Editor Quick Start in Unreal Engine20 setembro 2024 -
 Beware Of Fake 'HeartBleed Bug Remover Tool', Hijacks System with Malware20 setembro 2024
Beware Of Fake 'HeartBleed Bug Remover Tool', Hijacks System with Malware20 setembro 2024 -
 Adventures in WebRTC: Making Phone Calls from XMPP — JMP Blog20 setembro 2024
Adventures in WebRTC: Making Phone Calls from XMPP — JMP Blog20 setembro 2024
você pode gostar
-
 Little Witch Academia tem anime para TV anunciado20 setembro 2024
Little Witch Academia tem anime para TV anunciado20 setembro 2024 -
 In Another World With My Smartphone 2 Sakura Big Acrylic Stand (Anime Toy) Hi-Res image list20 setembro 2024
In Another World With My Smartphone 2 Sakura Big Acrylic Stand (Anime Toy) Hi-Res image list20 setembro 2024 -
Kahoot - How to create a game in Kahoot.20 setembro 2024
-
 Prideball -pokeball sprite (made on piskelapp) : r/lgbt20 setembro 2024
Prideball -pokeball sprite (made on piskelapp) : r/lgbt20 setembro 2024 -
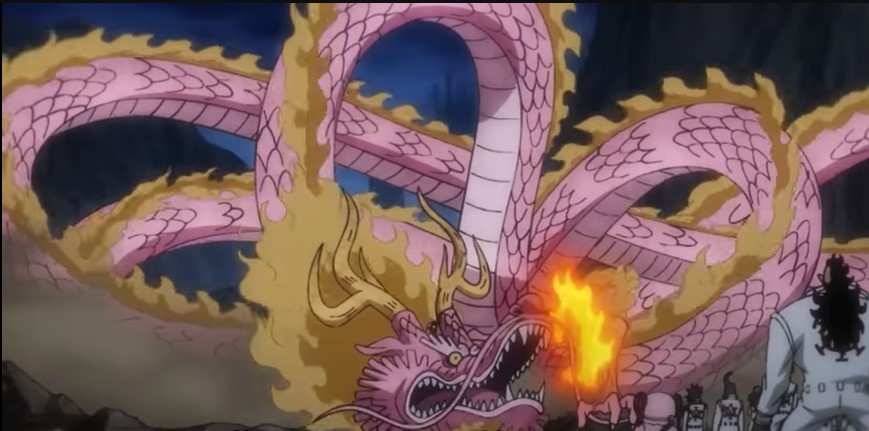 One Piece Episode 1049: Momo shows astonishing courage & transforms into a giant dragon20 setembro 2024
One Piece Episode 1049: Momo shows astonishing courage & transforms into a giant dragon20 setembro 2024 -
 Fala, Doente! LANCE! estreia podcast do Botafogo nesta terça-feira20 setembro 2024
Fala, Doente! LANCE! estreia podcast do Botafogo nesta terça-feira20 setembro 2024 -
 Jogo Killzone 3 PS3 - Plebeu Games - Tudo para Vídeo Game e Informática20 setembro 2024
Jogo Killzone 3 PS3 - Plebeu Games - Tudo para Vídeo Game e Informática20 setembro 2024 -
 SINUCA CAMPESTRE 1,90X1,17 m + TOTÓ LUXO 1,35X0,80 m + PING-PONG 220 setembro 2024
SINUCA CAMPESTRE 1,90X1,17 m + TOTÓ LUXO 1,35X0,80 m + PING-PONG 220 setembro 2024 -
Barbie Negra,tema novo. - Taty Festas mesas provençais20 setembro 2024
-
 combo de rumble e god20 setembro 2024
combo de rumble e god20 setembro 2024
